Exploitation - Свежие новости [ Фото в новостях ] | |
Ethereum’s Model Is Simply Exploitation Of The Working Class By The Wealthy, Says Analyst
Ethereum has come under fire for its economic model for several infringements against its original ethos. The reduction of miners’ rewards, burning of tokens, and the violation of the rule that “Code is Law” form part of the reason for criticisms. дальше »
2021-11-25 16:33 | |
|
|
How much did the Ethereum ecosystem lose to crypto-hacks in Q3
While the crypto-sector has seen exponential growth over the last few years, blockchain-related cyber crimes have also hiked. Cyber security issues and exploitation by hackers have been a major concerThe post How much did the Ethereum ecosystem lose to crypto-hacks in Q3 appeared first on AMBCrypto. дальше »
2021-10-28 21:00 | |
|
|
New York’s AG Stays Busy, Two Crypto Platforms Shutdown Others Under Investigation
Per a press release, the office of the New York Attorney General Letitia James revealed actions against two crypto platforms. The companies have been ordered to stop their operations to “protect New York investors from exploitation by high-risk virtual currency schemes”. дальше »
2021-10-18 19:50 | |
|
|
DeFi Protocol pNetwork Loses $12 Million In Tokenized Bitcoin
One of the threats that the crypto community face is the attack of cybercriminals. Many exchanges, projects, and apps often face one vulnerability exploitation or the other. Recently, BSC-based cross-chain pNetwork lost at least $12. дальше »
2021-9-25 00:00 | |
|
|
INS3 brings decentralized coverage to Polygon with 2,700 $ITF rewards per day
With the most recent DeFi exploits of the Polychain Network where the white-hatted hacker eventually did return the funds, DeFi is facing an exploitation problem on the network which if kept uncheckedThe post INS3 brings decentralized coverage to Polygon with 2,700 $ITF rewards per day appeared first on AMBCrypto. дальше »
2021-9-1 15:45 | |
|
|
INS3 Brings Decentralized Coverage to Polygon with 2,700 $ITF Per Day in Rewards
September 1st, 2021, Singapore :With the most recent DeFi exploit of the Polychain Network where the white-hatted hacker eventually did return the funds, DeFi is facing an exploitation problem on the network which if kept un-checked, will slowly but surely drain the industry of all total value locked. дальше »
2021-9-1 13:00 | |
|
|
Technical Problems Plague Ethereum Following Chain Split
Technical Problems Plague Ethereum Following Chain Split Ethereum experienced a barrage of chain splits caused by a bug in the old version of the software client, Geth. The failure of node operators to upgrade their software to the latest version is seen as a major trigger for the exploitation of the bug. Users have been […] дальше »
2021-8-29 00:32 | |
|
|
Poly Network Confirms Hacker Has Returned Most Of The Stolen Crypto
The crypto market has been rocked by the news of what might be the biggest DeFi hack in history. On August 10th, the exploitation on the Poly Network saw the hacker(s) make away with more than $600 million in crypto. дальше »
2021-8-14 20:00 | |
|
|
IRS is Developing ‘Exploitation Techniques’ to Break Into Crypto Wallets
According to its March report, the emergence and rapid adoption of cryptographic currencies have created a gap in digital forensic capabilities, and the decentralization and anonymity provided by cryptos are fostering an environment for the storage and exchange of value outside of the traditional purview of law enforcement and regulatory organizations. дальше »
2021-5-1 21:10 | |
|
|
SushiSwap Suffers Another Attack. Hacker Steals 81 Eth
This resulted from the exploitation of a system flaw leading to a successful hack. The perpetrator made off with part of the platform’s fees for the day. The SushiSwap Smart Contract Loophole The system vulnerability was spotted on Badger DAO token DIGG. дальше »
2021-1-29 22:27 | |
|
|
White Hat Hacker Steals $3M from Cover Protocol & Returns It Hours Later
Earlier on Monday, Cover Protocol suffered a major exploitation resulting in the loss of millions of dollars worth of COVER. Condensed down by Twitter user @Luciano_vPEPO, the hacker exploited an infinite minting bug on an incentives contract. дальше »
2020-12-28 19:57 | |
|
|
DOJ Wants Exceptions for End-to-End Encryption, Citing Child Exploitation
The US Department of Justice says it’s wary of End-to-End Encryption being used for child sex trafficking. Though it acknowledges encryption’s pluses, when and how exceptions could be made, remains unclear. дальше »
2020-10-13 21:00 | |
|
|
$RMPL Launches, Revolutionizing the Cryptocurrency Market with a Decentralized Elastic Supply Model
Announcing the official launch of $RMPL, an ERC20 cryptocurrency with an elastic supply model, redesigned to solve unfair market manipulation and exploitation. $RMPL is currently on Uniswap, and will soon be released on several popular cryptocurrency exchanges. дальше »
2020-8-17 23:30 | |
|
|
Much of Russia’s Blockchain Voter Data Is Now for Sale on the Dark Web
Many Russian citizens now face exploitation on the dark web after their Blockchain voting data was accidentally leaked in early July. дальше »
2020-8-7 19:40 | |
|
|
Ledger Hardware Wallet to Issue Exploit Fix to Prevent Users from Sending BTC on Accident
According to a blog published by Mo Nokhbeh, a crypto software researcher, the Ledger Wallet app is in danger of exploitation due to a vulnerability that has persisted on the platform since 2019. According to Mo, a user can send Bitcoin (BTC) instead of other Bitcoin forks such as the BTC testnets, Litecoin, Bitcoin Cash […] дальше »
2020-8-6 21:24 | |
|
|
US Court Tosses Appeal in Child Exploitation Case; Accessing Coinbase Account Didn’t Violate Fourth Amendment Rights
Richard Gratkowski, convicted of purchasing and receiving child pornography, and accessing websites with an intent to access child porn, was sentenced to 70 months in prison and ten years of probation. дальше »
2020-7-3 23:47 | |
|
|
Defi Protocol, Balancer (BAL) Community Votes On Updates To Prevent ‘Exploitation By Big Players’
Recent reports of FTX exchange ‘gaming' the Balancer Labs governance token, BAL, issuance raised a vote to quickly fix the platform to prevent “useless liquidity” from gaining rewards. дальше »
2020-6-25 17:37 | |
|
|
Japanese Non-Profit to Use Blockchain for Cobalt Tracing, Aims to Fight Child Labor
An Amnesty International finding shows that children–sometimes as young as seven, are toiling in cobalt mines in the Democratic Republic of the Congo (DRC), central Africa. Far from the gleaming surfaces of modern touch screen devices that rely on batteries, the inhalation of cobalt dust and child labor exploitation for the estimated 40,000 children illegally workingRead MoreRead More. дальше »
2020-6-20 01:07 | |
|
|
Carl Menger: The Nature and Origin of Money
In the early stages of trade, when economizing individuals are only slowly awakening to knowledge of the economic gains that can be derived from exploitation of existing exchange opportunities, their attention is, in keeping with the simplicity of all cultural beginnings, directed only to the most obvious of these opportunities. дальше »
2020-5-24 23:02 | |
|
|
Huobi Korea Delists Monero Over Nth Room Case, Bithumb May Follow
Reports have emerged that participants in a Korean-based sexual exploitation ring used Monero for criminal acts. As a result, Bithumb is considering delisting the cryptocurrency. Huobi has already dropped it from its Korean exchange. дальше »
2020-4-11 16:30 | |
|
|
Blockchain Tech Was Made to Combat Rising Identity Theft in Digital World [Opinion]
Numerous reports have come from both inside and outside the industry about how large swathes of citizens’ data are at risk or being exploited. In such a time, when the world is dependent on digital data, cryptocurrencies and blockchain technology stand as a bulwark against surveillance and data exploitation. дальше »
2020-3-28 22:15 | |
|
|
DeFi Apps Represent 24/7 Multi-Million Dollar Hacker Honeypots
A recent smart contract exploit resulted in the loss of 1,193 ETH. The incident has prompted questioning of the security of the rapidly evolving DeFi sector. Over the weekend, the exploitation of a smart contract vulnerability forced developers at Ethereum-based app Fulcrum to partially disable its smart contract. дальше »
2020-2-23 19:10 | |
|
|
DEX Volume Soars But Bzx Exploit Raises Questions About ‘Decentralization Theatre’
As the decentralized finance juggernaut rolls inexorably forward, the exploitation of defi project Bzx – in which $350K, or around 2% of total assets was taken – has called the decentralization of the industry into doubt. дальше »
2020-2-18 02:10 | |
|
|
UN Migration Agency Leverages Blockchain to Tackle Hong Kong Migrant Worker Problem
The International Organization for Migration (IOM) – the United Nations Migration Agency – in partnership with blockchain startup Diginex – on December 16, 2019, announced the launch of a blockchain-based tool to mitigate the exploitation of migrant domestic workers in Hong Kong SAR, China. дальше »
2019-12-17 18:00 | |
|
|
UN to Prevent Hong Kong Migrant Workers Exploitation with Blockchain
UN-led International Organization for Migration and Diginex plan to use blockchain to prevent the exploitation of migrant workers
дальше »2019-12-17 20:03 | |
|
|
UN agency to use Diginex blockchain technology to rid illegal fees charged to migrant workers
Diginex, a blockchain technology and financial services company, and the International Organization for Migration (IOM) – the United Nations Migration Agency – today announced the launch of a blockchain tool developed to prevent the exploitation of migrant domestic workers in Hong Kong SAR, China. дальше »
2019-12-16 14:36 | |
|
|
Coinbase Reveals How It Averted A Complex Hacking Attack Seeking To Extract Private Keys And Passwords
Coinbase’s security team has revealed that it managed to stop a complex phishing attack that sought to extract user private keys and passwords. In an official blog post the crypto exchange giant revealed that the incident involved the exploitation of two 0-day vulnerabilities on the Mozilla Firefox browser. According to the blog post, the first […] дальше »
2019-8-9 21:17 | |
|
|
Facebook open-sources APIs to help fight child exploitation and terrorist propaganda
Facebook today announced it’s open-sourcing two technologies that help it curb the spread of problematic content like child exploitation, terrorist propaganda, or graphic violence online. These technologies aid the social network in detecting identical and nearly identical photos and video in order to weed out content that’s been flagged as being in violation of its policies. дальше »
2019-8-2 08:50 | |
|
|
US tip-off leads to arrest after man buys child abuse imagery with cryptocurrency in Australia
An Australian man has been charged after authorities linked him to a cryptocurrency account used to buy child exploitation material. An investigation, following a tip off from US authorities in December last year, traced the account back to a 27-year-old man from Sydney. дальше »
2019-7-9 12:09 | |
|
|
From Exploitation to Collaboration: Nasdaq-Listed Firm’s Vision for the Future of Advertising
A Nasdaq-listed company says it is offering a blockchain-enabled alternative to “centralized authorities that perpetuate ad fraud, waste and abuse.” #SPONSORED
дальше »2019-6-20 18:33 | |
|
|
Cryptocurrency: Involvement of virtual assets among teens an adoption blessing or major exploitation?
Kin, a crypto-project based around messaging app Kik, recently made headlines as the organization launched the DefendCrypto. org dubbed fund against the US Securities and Exchange Commission [SEC]. дальше »
2019-6-3 04:00 | |
|
|
Report: North Korea May Exploit Southeast Asia’s Crypto Exchanges
North Korea could pose a threat to countries across Southeast Asia as it looks to exploit cryptocurrency exchanges due to gaps in regulatory frameworks, according to a new report. дальше »
2019-4-25 17:04 | |
|
|
YouTube’s ‘child safe’ app is crawling with videos advocating suicide, murder, and sexual exploitation
For nearly five minutes, the cartoon is predictable. Colorful characters with child-like voices act out the types of scenarios capable of reversing even the wildest tantrums, turning screaming toddlers into tiny, submissive humans. дальше »
2019-3-22 02:49 | |
|
|
Alexandria Ocasio-Cortez Declares Victory after Amazon Yanks HQ2 from New York
US House Rep. Alexandria Ocasio-Cortez wasted no time in declaring victory after Amazon backed out of a $3 billion deal that would have seen the Jeff Bezos-led tech conglomerate establish its much-coveted HQ2 in New York. дальше »
2019-2-15 22:06 | |
|
|
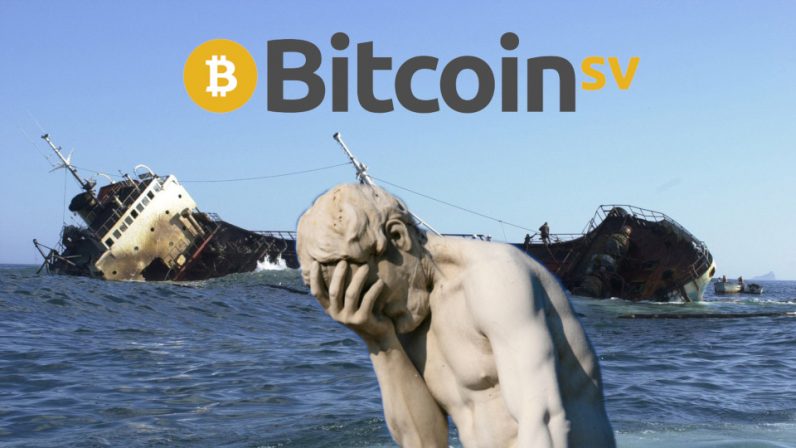
BitcoinSV ‘feature’ exploited to store child abuse imagery on the blockchain
A change to the Bitcoin Satoshi’s Vision (BSV) protocol has inadvertently led to child exploitation material being posted to its blockchain, forcing apps and block explorers into actively monitoring the network for illegal content. дальше »
2019-2-4 19:22 | |
|
|