Новости о Your Exploit [ Фото новости ] [ Свежие новости ] | |
Binance CEO had WeChat hacked by cellphone exploit that likely leaves your own crypto exposed
Binance co-CEO Yi He said her WeChat account was hijacked on Dec. 10 after a cell number tied to the profile was reclaimed and could not be recovered at first. The account was later restored after Binance worked with WeChat’s security team, according to a spokesperson cited the same day. дальше »
2025-12-11 00:00 | |
|
|
$908K USDC stolen, 458 days after approval: 'Your wallet security matters!'
Key Takeaways A user lost nearly $1 million in USDC to a scam tied to a malicious contract signed 458 days earlier. Experts warn that this delayed exploit trend is becoming a go-to strategy for cryptThe post $908K USDC stolen, 458 days after approval: 'Your wallet security matters!' appeared first on AMBCrypto. дальше »
2025-8-4 01:00 | |
|
|
Is your crypto security at risk after the leak of 16 billion logins?
How vulnerable is crypto security when cloud storage and Elasticsearch remain widely exposed? Experts warn that real-time threats like PylangGhost may exploit stolen credentials to compromise cThe post Is your crypto security at risk after the leak of 16 billion logins? appeared first on AMBCrypto. дальше »
2025-6-21 19:00 | |
|
|
Be warned! Hackers are abusing API keys and stealing your funds
Cybercriminals always find a way to exploit the loopholes present in the cryptocurrency market. As the blockchain space is gaining more interest and popularity, the technology is advancing at an unbelievable pace, leading to more complexity and a chance of error. дальше »
2021-6-13 19:25 | |
|
|
The Daily: Privacy Coin Strength Debated, Hardware Wallet Exploit Demonstrated
In Tuesday’s edition of The Daily, we detail the theoretical vulnerability found in the Coldcard crypto wallet, coming just one month after its manufacturer ridiculed the flaw found in other hardware wallets. дальше »
2019-1-29 17:00 | |
|
|
Apple temporarily disables group FaceTime to fix a bug that lets you eavesdrop on your contacts
There was chaos on the internet late last night after 9to5Mac discovered a bug in Apple’s FaceTime video calling app that let you hear other person’s voice even before they answered your call. According to the report, a user running iOS 12. дальше »
2019-1-29 08:16 | |
|
|
Neutrino: A Privacy-Preserving Light Wallet Protocol
Lightning is all the rage these days and, while it's an exciting development, users currently have to have a full node running in order to transact in it. In this article, I'm going to introduce Neutrino, a new protocol for light clients to get the data that they need while preserving privacy and without trusting a central server. дальше »
2019-1-4 21:11 | |
|
|
Did you #DeleteFacebook? Shady players can still exploit your data
Caring about our online privacy might be popular right now, but on a wider level, it’s not as easy as we think to escape the hole we’ve dug ourselves into. дальше »
2019-1-2 14:21 | |
|
|
PS4s are being bricked by a chat exploit – here’s how you can stay safe
PlayStation 4 owners recently began reporting a strange messaging exploit, one which has already been allegedly weaponized to brick their consoles. Sony is working to fix the problem, but in the meantime, everyone just set your messages to private. дальше »
2018-10-16 21:49 | |
|
|
Coinberry Traders Keep Control of Keys With BRD Crypto Wallet Integration
Cryptocurrency trading service Coinberry has partnered with BRD, a secure bitcoin wallet service, in a deal that promises to bring BRD's Canadian users onto Coinberry's no-fee trading platform. дальше »
2018-8-21 18:52 | |
|
|
This browser extension makes it harder for Facebook advertisers to target you
A trio of Mozilla Fellows recently released a browser extension designed to keep Facebook‘s advertisers from pigeonholing you. We’ve argued that Facebook should pay users for their data, but in lieu of that, at least this tool makes it harder for the social network to exploit it. дальше »
2018-8-17 19:31 | |
|
|
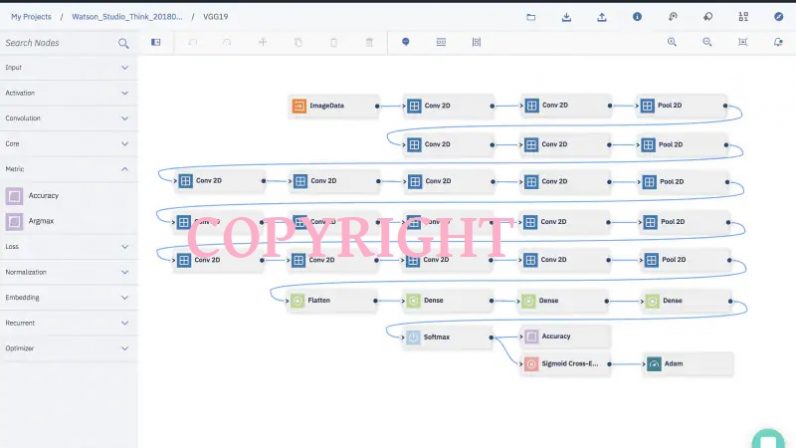
IBM came up with a watermark for neural networks
The creation and development of a robust neural network is a labor-intensive and time consuming endeavor. That’s why a team of IBM researchers recently developed a way for AI developers to protect their intellectual property. дальше »
2018-7-20 18:52 | |
|
|
Op Ed: Addressing the Threat of Cryptomining Malware
One major class of attacks to hit the hacking landscape recently is cryptomining. While cryptomining on its own supports a good cause when being done consciously, it also allows nefarious actors to make a lot of money fast, and, with the sheer number of cryptocurrencies available to mine, it is becoming a popular choice for attackers. дальше »
2018-7-18 23:18 | |
|
|