Новости о Security Extra [ Фото новости ] [ Свежие новости ] | |
Polygon and Aleph.im Join Forces to Provide Extra Security for NFTs and dApps
Their integration with the ETH scaling project hopes to provide extra security and permanence for NFTs, marketplaces, and dApps running on Polygon. The post Polygon and Aleph.im Join Forces to Provide Extra Security for NFTs and dApps appeared first on BeInCrypto. дальше »
2021-5-26 16:00 | |
|
|
Apple steps in to automatically remove Zoom’s risky software from Macs
Apple has pushed a silent update to Mac users to remove the web server sneakily installed by popular video conference app Zoom, TechCrunch reports. Earlier this week, a disclosure by security researcher Jonathan Leitschuh revealed how Zoom installed a secret local web server on Mac devices — with an intent to save an extra click — but left users vulnerable by making it possible for an attacker to hijack their webcams. дальше »
2019-7-11 08:41 | |
|
|
Sidechains vs Plasma vs Sharding
Special thanks to Jinglan Wang for review and feedback One question that often comes up is: how exactly is sharding different from sidechains or Plasma? All three architectures seem to involve a hub-and-spoke architecture with a central “main chain” that serves as the consensus backbone of the system, and a set of “child” chains containing actual user-level transactions. дальше »
2019-6-14 04:03 | |
|
|
Save an extra 25% on Private Internet Access VPN subscriptions this Memorial Day
So when you can score a deal on essential online security from a heritage brand, it’s time to jump on that offer. Right now, you can secure a one-year PIA subscription for $37. 49 (Orig. $119. дальше »
2019-5-26 15:00 | |
|
|
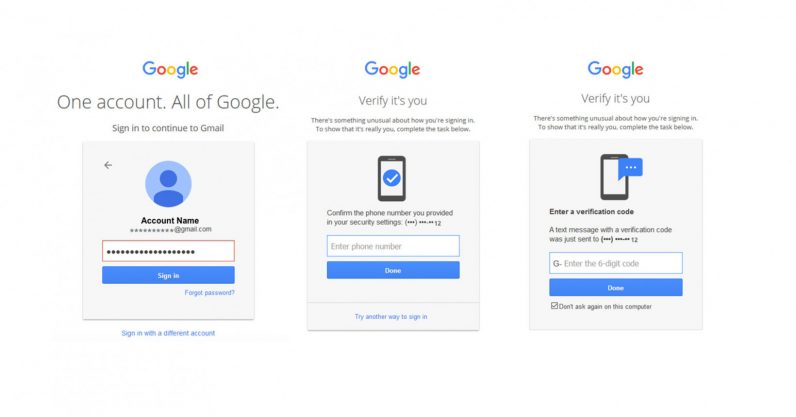
Google data shows 2-factor authentication blocks 100% of automated bot hacks
Two-factor authentication is annoying. Getting flustered because you have to find your phone and tap on a prompt every time you log into your accounts from a new device is peak first-world problems. дальше »
2019-5-24 01:17 | |
|
|
Binance Partners with Blockchain Security Firm CipherTrace, Bolsters AML Measures
Malta-based cryptocurrency exchange Binance announced that they have partnered with blockchain security firm CipherTrace to bolster their anti-money laundering (AML) measures. This according to a Binance Blog post on April 11, 2019. дальше »
2019-4-12 11:45 | |
|
|
Report Claims That “Sextortionists” Absconded With Over $300,000 in Crypto in 2018
Most cyberattacks in the crypto space involve hackers finding a way around the security of crypto exchange platforms and gaining access to users’ funds. Last year saw the entry of a new breed of cyber extortionists that seems to be gaining ground, so much so that they were able to steal over $300,000 in bitcoin (BTC) tokens in 2018. дальше »
2019-3-1 18:10 | |
|
|
Securypto ICO
Securypto is a Zerocoin, masternode-based blockchain project focused on anonymous storage & transferring of encrypted data. A technology that agitates the market by allowing the following: Monetization of anonymous content distribution, creating a new emerging market. дальше »
2019-1-26 17:03 | |
|
|
How Bitcoin Investors Can Ensure Extra Security and Privacy When Trading Crypto Assets Using VPNs
Online security is one of the largest problems that internet users are facing today, and this has been an issue for years now. While an average user has the potential to get exposed to online threats such as malware or hackers, the situation may be even worse for cryptocurrency traders. Ever since cryptocurrencies exploded in […] дальше »
2019-1-19 20:22 | |
|
|
Microsoft is euthanizing Windows 10 Mobile in 2019
Just a few days after announcing it would stop supporting Windows 7 soon, Microsoft is sounding the death knell for another of its products: Windows 10 Mobile. Starting December 10, 2019 your devices will no longer be able to receive security or software updates on the OS, and Microsoft will no longer provide support should issues arise. дальше »
2019-1-18 21:57 | |
|
|
Why Ohio’s State Treasurer Backs Decision to Accept BTC For Tax Payments
As tax season is rapidly approaching, some states, like Ohio, have decided to set a new standard for the rest of the country to follow. Back in November, Ohio became the first state in the U. дальше »
2019-1-3 20:53 | |
|
|
New Shakepay Feature Turns Your Spare Change Into Bitcoin
Mobile cryptocurrency exchange and peer-to-peer wallet Shakepay has announced a new product that allows its Canadian customers to buy bitcoin with spare change. Dubbed "ShakePay Change," the pre-launch of the service was announced in a Medium post. дальше »
2018-12-18 02:32 | |
|
|
Crypto Holiday Guide: Gifts for Every Bitcoiner on Your Shopping List
The holiday season is here. And even if crypto prices are on the coal heap, you can still have fun spreading some holiday bitcoin cheer. For the bitcoiners in your life, this could mean a crypto-related gift as a token of solidarity. дальше »
2018-12-12 23:22 | |
|
|
Etherscan Users Can now Validate Transactions on Infura, MyCrypto, and MyEtherWallet
Infura, MyCrypto, and MyEtherWallet partner to allow an extra layer of security by introducing verified transactions for Etherscan users. What Is EthValidate? The development of the Ethereum platform is moving ahead at full steam despite the drop in ETH price. дальше »
2018-12-4 16:00 | |
|
|
Thomson Reuters Partners With Startup for Next Level Derivatives Exchange
Thomson Reuters (TR) provides trusted data and information to professionals across the legal, tax and accounting, and news and media industries. Operating in more than 100 countries, TR lists its shares on both the New York Stock Exchange (NYSE) and Toronto Stock Exchange (TSE). дальше »
2018-10-30 00:44 | |
|
|
AT&T Dives Into Blockchain Solutions With Microsoft Azure, IBM Blockchain
Internet and phone giant AT&T has designed a set of blockchain solutions compatible with both IBM and Microsoft technology to help customers reduce risks and costs and solve other complex business problems. дальше »
2018-9-28 00:04 | |
|
|
Cryptocurrency That Works Without Internet, mCoin Launches In Africa
London-based ONEm Communications has announced the launch of its mCoin program across Africa. Designed to be a hybrid currency, mCoin is a digital currency that can be transferred over text or through the smartphone app. дальше »
2018-9-25 21:26 | |
|
|
ShapeShift to Add Multi-Crypto Swapping Tool to Its Exchange Platform
On August 8, 2018, ShapeShiftAG, the parent company of ShapeShift. io, one of the world's largest decentralized cryptocurrency exchanges, announced its acquisition of Bitfract, a blockchain software startup based in Austin, Texas. дальше »
2018-8-10 19:33 | |
|
|
It Turns Out Monero’s Privacy Coin Wasn’t So Private After All
Reports out today highlight yet another security vulnerability within Monero XMR, a cryptocurrency designed for optimum privacy. Now we already know of the associations between Monero and malicious mining, but this marks another example of how XMR traders and investors have been put at risk, simply due to the markup of the currency. дальше »
2018-8-2 17:00 | |
|
|
Monero wallet vulnerability made it possible to steal XMR from exchanges
It appears popular cryptocurrency Monero, often praised for its privacy functions, was riddled with security vulnerabilities – one of which allowed hackers to steal coins directly from the wallets of exchange desks. дальше »
2018-8-2 15:16 | |
|
|
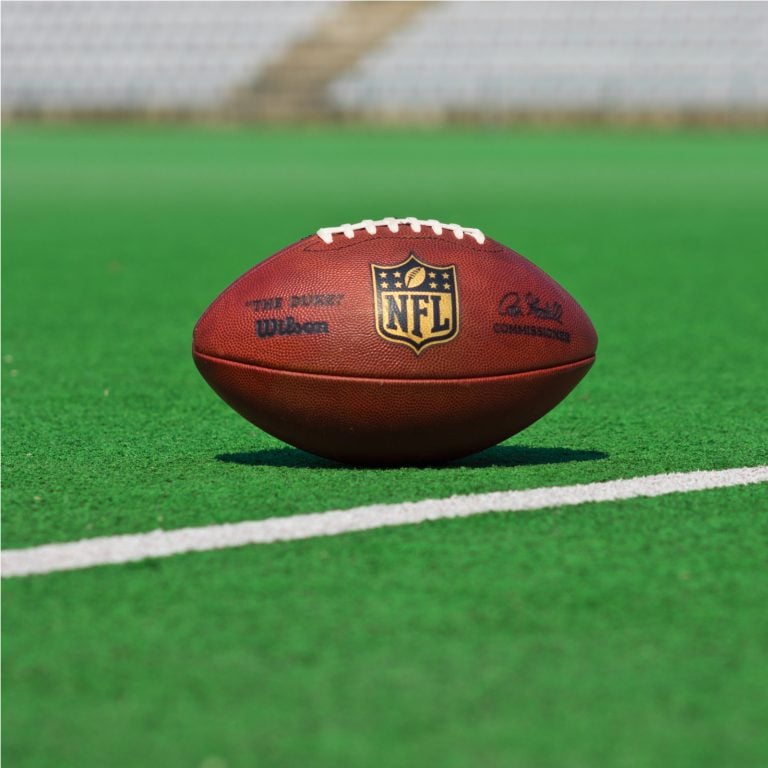
The Daily: NFL Players to Earn Crypto, McDonald’s Unveils Maccoin, Bill Clinton at Swell
In today’s edition of Bitcoin in Brief we cover the stories about how NFL players can start to earn some extra cryptocurrency, McDonald’s latest publicity stunt called Maccoin, former US president Bill Clinton to speak at Swell by Ripple, and Binance’s acquisition of Trust Wallet. дальше »
2018-8-1 11:55 | |
|
|
Facebook will spend $10M on CEO Mark Zuckerberg’s private jets and security
The social network yesterday filed a report with the SEC, which disclosed CEO Mark Zuckerberg’s security allowance. All those extra trips to testify in front of Congress this year must have taken their toll, because he’s now allotted $10 million. дальше »
2018-7-27 22:13 | |
|
|
Governance, Part 2: Plutocracy Is Still Bad
Coin holder voting, both for governance of technical features, and for more extensive use cases like deciding who runs validator nodes and who receives money from development bounty funds, is unfortunately continuing to be popular, and so it seems worthwhile for me to write another post explaining why I (and Vlad Zamfir and others) do not consider it wise for Ethereum (or really, any base-layer blockchain) to start adopting these kinds of mechanisms in a tightly coupled form in any significant way. дальше »
2018-7-21 23:03 | |
|
|