Новости о Your Work [ Фото новости ] [ Свежие новости ] | |
What Is A Bitcoin Address: How ‘Blockchain Bank Account Numbers’ Work
Similar to a bank account, a bitcoin address is where you receive and transfer your bitcoins. Without it, there’s no way you would receive or send bitcoins. After all, your senders will need that address to accurately send you bitcoins. дальше »
2018-8-3 16:47 | |
|
|
Bodhi Bets on the Decentralized Prediction Marketplace
As with brick-and-mortar industries that are slowly fading away to the globalism of the online world, so too will the traditional prediction market industry have to innovate to keep up with the sheer efficiency, reliability and security that the decentralized prediction markets promise to bring. дальше »
2018-7-31 15:58 | |
|
|
“He told me that my ‘project’ is cute and let’s discuss it in bed.”
“He told me that my ‘project’ is cute and let’s discuss it in bed. ” “He suggested I should start sleeping with him in order to learn more about the ecosystem and succeed. ” “I was at a work event at a hotel talking to a VC about my company. дальше »
2018-7-31 11:32 | |
|
|
How Blockchain Promotes International Trade, Identity and Financial Inclusion
International trade, people without identity and financial exclusion are global development areas that stand to be radically improved with blockchain technology, according to Michelle Chivunga, regional advisor for the British Blockchain Association. дальше »
2018-7-31 19:50 | |
|
|
Comino Brings Plug-and-Play Simplicity to Cryptocurrency Mining [Interview]
As interest in cryptocurrencies continues to grow, so too does interest in cryptocurrency mining. Unfortunately, there can be a significant learning curve involved. Comino aims to change that with their line of completely pre-assembled devices that work with plug-and-play simplicity. дальше »
2018-7-29 23:00 | |
|
|
Richard Milam: The Global Impact Of AI As It Applies To The Banking Industry – Not Billions But Trillions
You may have heard about a robot called ‘Flippy’ that makes hamburgers instead of Phil, your average fast food worker. Robots are infiltrating the workplace, including banks. Robots can enhance work, productivity while reducing costs due to errors. дальше »
2018-7-28 18:13 | |
|
|
Windows 10 will soon prevent updates from unexpectedly rebooting your PC
Since the launch of Windows 10 some three years ago, Microsoft has been catching flak for the OS’ updates hijacking users’ workflows and rebooting their PCs – causing people to lose their unsaved work. дальше »
2018-7-26 10:50 | |
|
|
How Does The Bitcoin Trading Master: Simulator Crypto Game Work
Are you interested in trading cryptocurrencies? If you are, the new Bitcoin Trading Master: Simulator, which is available on early access on Steam right now, can be a good chance for you to learn how to trade Bitcoin without actually having to do it first and risk losing your money. Read our review. What Is […] дальше »
2018-7-24 15:55 | |
|
|
Why You Need To Check Out Megapawnshop
What is Megapawnshop? Megapawnshop is a microfinance company that will let you get a loan against Bitcoin without the hassle. Providing lending services for over six years, Megapawnshop is the leading financial institution for your crypto loans. дальше »
2018-7-23 13:15 | |
|
|
You can’t achieve long term profits without knowing how your employees feel
Does your company get a good return on all the time and money it invests in leadership development? Despite the millions spent on developing leaders, many employees — perhaps even most — are disengaged from their work and not giving it their best shot. дальше »
2018-7-22 11:30 | |
|
|
STARKs, Part I: Proofs with Polynomials
Special thanks to Eli Ben-Sasson for ongoing help, explanations and review, coming up with some of the examples used in this post, and most crucially of all inventing a lot of this stuff; thanks to Hsiao-wei Wang for reviewing Hopefully many people by now have heard of ZK-SNARKs, the general-purpose succinct zero knowledge proof technology that can be used for all sorts of usecases ranging from verifiable computation to privacy-preserving cryptocurrency. дальше »
2018-7-21 23:03 | |
|
|
5 Fierce Facts About Cybersecurity You Probably Don’t Want to Hear
It’s hard work running a business. It almost makes you ache for a simpler time when all you had to worry about was shoplifters stealing your goods. Now you’ve got confidential data, trade secrets, and, of course, plenty of money at stake. дальше »
2018-7-21 00:00 | |
|
|
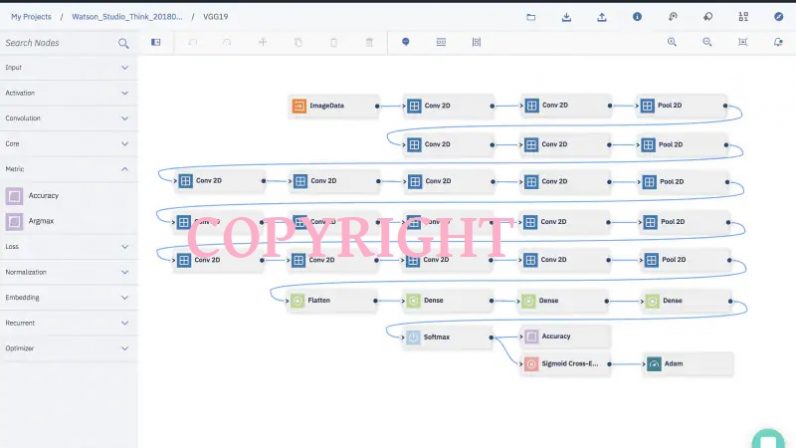
IBM came up with a watermark for neural networks
The creation and development of a robust neural network is a labor-intensive and time consuming endeavor. That’s why a team of IBM researchers recently developed a way for AI developers to protect their intellectual property. дальше »
2018-7-20 18:52 | |
|
|
Op Ed: Addressing the Threat of Cryptomining Malware
One major class of attacks to hit the hacking landscape recently is cryptomining. While cryptomining on its own supports a good cause when being done consciously, it also allows nefarious actors to make a lot of money fast, and, with the sheer number of cryptocurrencies available to mine, it is becoming a popular choice for attackers. дальше »
2018-7-18 23:18 | |
|
|
How Digital Signatures and Hashing Protect Your Transactions
Digital Signatures and Hashing Digital signatures and cryptographic hash functions comprise the secret sauce that makes cryptocurrency work. They put the crypto into currency, so to speak. Your digital signature proves you have the private key that claims ownership of… The post How Digital Signatures and Hashing Protect Your Transactions appeared first on CoinCentral. дальше »
2018-7-12 14:47 | |
|
|
If You’re Living In Australia, Hiding Your Crypto Offshore Doesn’t Mean You’ll Avoid Tax
People hate paying tax on their income. People really hate paying tax on their crypto too. Cryptocurrency was designed to be decentralised and away from the government, so why on earth should the government profit from our hard work and investments? There are ways around crypto tax, for now. дальше »
2018-7-9 17:00 | |
|
|
BlockShow by Cointelegraph is Debuting in Vegas with BlockShow Americas 2018
Shortly after a successful comeback to Germany with BlockShow Europe 2018, the team gets to work again and announces BlockShow Americas 2018 - the next 2-day show and the very first one to be held in USA. дальше »
2018-7-6 14:58 | |
|
|
Decommissioned Swiss Army Bunkers Can Keep Your Bitcoins Safe
The banking sector appears almost smitten by Bitcoin and other cryptocurrencies these days. Although there is still plenty of work to be done, it seems Xapo has some big plans. Using old Swiss army bunkers for Bitcoin-related purposes raises a lot of questions. дальше »
2018-6-30 21:00 | |
|
|
Op Ed: Utility Token? Why You’re Still Better Off as a Security
The SEC’s proclamation that ether (ETH) is not a security has sparked some celebration amongst the cryptocurrency community. Regulatory clarity is always a good thing, but ICO operators shouldn’t see this as a reason to put the champagne on ice. дальше »
2018-6-26 19:36 | |
|
|
Centralized exchanges are throwing the Crypto Promise to the wind!
With such a terrible track record, why would anyone still work with crypto exchanges? That is where crypto exchanges come in, and they are especially valuable to day traders. Crypto exchanges also take care of storing your money, much like a bank would. дальше »
2018-6-24 17:36 | |
|
|
Jeff Garzik on His Newest Venture and Keeping Time With an Evolving Space
Jeff Garzik first tuned the world into his latest venture in the fall of 2017. The Bloq co-founder unveiled Metronome (MET), a cryptocurrency he founded alongside Matthew Roszak, at the Las Vegas Money 20/20 conference in late October, and the project caught the attention of Bloomberg and Fortune at the time. дальше »
2018-6-16 23:51 | |
|
|
Till Death Do Us Fork: Planning for Cryptoasset Inheritance
For many, the experience of adding crypto coins to their financial portfolios has proven to be the thrill of a lifetime. As a new type of holding with a unique set of tools and rules, cryptocurrency is wealth with its own wow factor. дальше »
2018-6-15 18:54 | |
|
|
On Radical Markets
Recently I had the fortune to have received an advance copy of Eric Posner and Glen Weyl’s new book, Radical Markets, which could be best described as an interesting new way of looking at the subject that is sometimes called “political economy” - tackling the big questions of how markets and politics and society intersect. дальше »
2018-7-21 04:03 | |
|
|