Новости о Security Next [ Фото новости ] [ Свежие новости ] | |
Researchers show how data science techniques can find Twitter ‘amplification bots’
Researchers from Duo Security, an authentication services company owned by Cisco Systems, have published a blog post that explains how to methodically identify “amplification bots. ” These are defined as automated Twitter accounts that purely exist to artificially amplify the reach of content through retweets and likes. дальше »
2018-12-11 17:00 | |
|
|
Study: The NHS is desperately in need of infosec professionals
The UK’s NHS health system is desperately short of information security professionals, research from infosec consultancy Redscan shows. The firm found that NHS trusts typically have just one member of staff with cybersecurity credentials per 2,628 employees. дальше »
2018-12-11 03:00 | |
|
|
Google+ will die 4 months sooner thanks to new bug affecting 52 million users
After announcing in October it would be shuttering Google+, its little-loved social media site, Google today announced that, thanks to yet another security flaw, the end would have to come much sooner than originally expected. дальше »
2018-12-10 21:38 | |
|
|
MasterCard wants to make electronic payments anonymous… with blockchain
Just as the US Department of Homeland Security announced plans to develop forensic techniques to deanonymize cryptocurrency transactions, MasterCard has thrown a spanner in the works with plans for the exact opposite. дальше »
2018-12-7 18:01 | |
|
|
Mozilla and ThingsCon launch certification mark for secure IoT devices
Mozilla and ThinksCon today announced the launch of the Trustable Technology Mark, which will help consumers determine if their latest “smart” home gizmo is designed with privacy and security in mind. дальше »
2018-12-6 16:00 | |
|
|
German artists brilliantly honeypot ‘Nazis’ into exposing themselves and their friends
In an elaborate scheme, the German political art collective Center for Political Beauty (ZPS) tricked thousands of potential far-right supporters to unknowingly reveal themselves. Earlier this week ZPS set up a site where people could identify far-right demonstrators in exchange for money. дальше »
2018-12-6 13:02 | |
|
|
South Korea Is Trialing Blockchain Voting — Here’s What That Means
South Korea will test out a new blockchain voting system this month, sources close to the developments have confirmed to Bitcoin Magazine. Developed by the country’s National Election Commission (NEC) and its Ministry of Science and ICT, the distributed ledger system is based on IBM’s Hyperledger Fabric and will be used to authenticate voters and save voting results in real time. дальше »
2018-12-4 21:41 | |
|
|
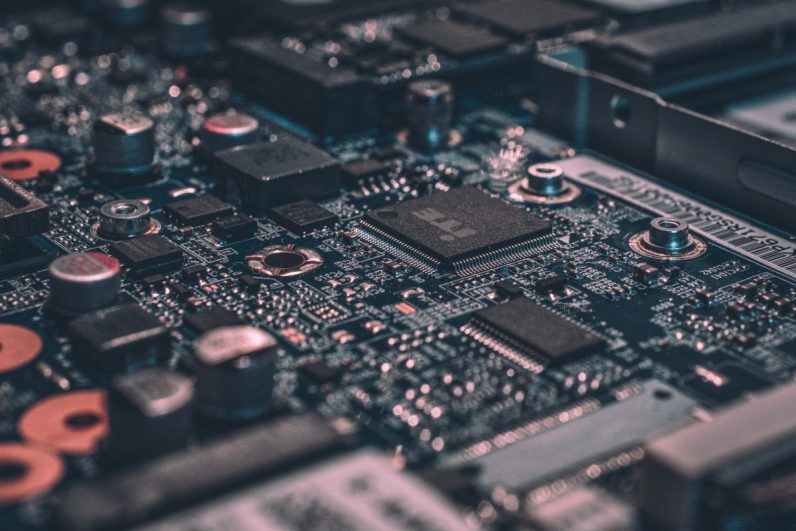
415,000 routers worldwide hijacked to secretly mine cryptocurrency
Researchers have discovered over 415,000 routers across the globe have been infected with malware designed to steal their computing power and secretly mine cryptocurrency. The attack, which is still ongoing, affects MikroTik routers in particular. дальше »
2018-12-4 20:38 | |
|
|
Top IoT messaging protocols are laughably insecure, Trend Micro research shows
Japanese cybersecurity firm Trend Micro today published a report on the state of IoT security. The company found that two of the leading machine-to-machine (M2M) protocols have inherent design issues, and are frequently deployed in an insecure manner. дальше »
2018-12-4 17:27 | |
|
|
US government building tools to deanonymize anonymous cryptocurrencies
If you thought you were safe using privacy coins like Zcash and Monero you might want to think again. It appears that the US Department of Homeland Security (DoHS) is looking to develop forensic analysis techniques for privacy-focused cryptocurrencies like Zcash and Monero, according to a pre-solicitation document spotted by The Block. дальше »
2018-12-4 15:19 | |
|
|
Security token offerings are illegal in Beijing, finance watchdog says
China has remained vigilant toward the fledgling blockchain and cryptocurrency industry for a while – and things might be about to get even worse. Beijing has declared security token offerings (STOs) illegal. дальше »
2018-12-3 14:39 | |
|
|
BEXAM ICO
BEXAM is built on a new consensus-building algorithm called Proof of Rounds. PoR reconciles high speed and scalability with high security. Our next generation blockchain technology finally meets the specifications required for the implementation of blockchain into core centralized systems of large-scale businesses. дальше »
2018-12-3 13:35 | |
|
|
AI-generated fingerprints could soon fool biometric systems
Research led by two top universities has shed doubt on whether biometric security systems, on their own, can protect our most sensitive data. Humans are notoriously bad at creating secure passwords. дальше »
2018-11-29 06:52 | |
|
|
Botnet operators ditch DDoS attacks for cryptocurrency mining malware
Leading cybersecurity unit Kaspersky Labs has warned hackers are “reprofiling” the world’s most well-known botnets en masse in order to spread their cryptocurrency mining malware as widely as possible. дальше »
2018-11-28 18:56 | |
|
|
SEC chairman crushes hopes of Bitcoin ETFs once again
A week after the Securities and Exchange Commission (SEC) dished out massive fines and closed a prominent “decentralized” exchange, its chairman is dashing hopes for Bitcoin Exchange Traded Funds (ETFs) one more time. дальше »
2018-11-28 14:37 | |
|
|
Five Reasons Why Security Tokens are Taking Over the Cryptocurrency Space
Security and asset-backed tokens appear to be one of the prominent points on interest in the emerging cryptocurrency landscape. Such is the popularity of the sector that some experts predict that security tokens could become a multitrillion-dollar market within the next decade. дальше »
2018-11-28 06:34 | |
|
|
You need a VPN? We got deals on five of ‘em
You may not think you need a VPN. If you’re laboring under that assumption, we’d like to counter with this: You’re wrong. If your IP isn’t masked by a VPN connection, there’s a good chance your Internet service provider is compiling information on you. дальше »
2018-11-27 19:52 | |
|
|
Po.et’s Mainnet Launch Puts Creative Content Data on the Bitcoin Blockchain
Disclaimer: The parent company of Bitcoin Magazine, BTC Media, LLC, is an affiliate of Po. et. Today, November 27, 2018, the Po. et team has taken its next step toward the verifiable web as it officially launches its proof-of-existence protocol on the Bitcoin mainnet. дальше »
2018-11-28 17:40 | |
|
|
Sketchy apps with more than 2 billion installs allegedly involved in click fraud
Chinese app developer Cheetah Mobile has been accused of running a major click fraud scam, using its Android apps which have a combined install base of more than 2 billion. BuzzFeed News reported that research from mobile analytics company Kochava found eight apps – seven from Cheetah Mobile and one from Kika Tech – misusing Android user permissions to gain referral earnings from app installs. дальше »
2018-11-27 13:13 | |
|
|
The frustratingly simple techniques of ‘human hacking’ — and how to fight them
Technology has changed the meaning of how we interpret security and privacy in this digital millennium. We’ve made tools that can prevent major vulnerabilities, with years of research, and debugging, to finally prevent disruptions in our workflow from occurring. дальше »
2018-11-24 21:30 | |
|
|
The entire cryptocurrency market is now worth less than McDonald’s
Chew on this: the entire cryptocurrency market now has a smaller market cap than fast food titan McDonald’s. The total worth of the cryptocurrency market has fallen to $139. 7 million – a staggering 80-percent-plus downswing compared to a $819 billion market cap in January 2018. дальше »
2018-11-23 16:46 | |
|
|
500,000 Android users downloaded malware made by one developer
Android malware has been on the rise over the past couple of years, we’ve just seen one of the worst attacks of this kind. ESET security researcher Lukas Stefanko found 13 apps with malware on the Play store, and said that more than 560,000 people downloaded these apps before Google took them down. дальше »
2018-11-21 14:09 | |
|
|
Facebook hack proves we need new user authentication methods
Just when you thought Facebook has put the worst of its troubles behind, the social media giant revealed on Friday that it had experienced a new security incident that possibly affected 90 million users. дальше »
2018-11-20 17:28 | |
|
|
Hackers infect official Make-A-Wish site with cryptocurrency mining malware
It seems crypto-jackers have absolutely no ethical standards. After governments, universities, and technology giants, even charitable organizations are finding themselves at the receiving end of cryptocurrency malware. дальше »
2018-11-19 19:42 | |
|
|
Drone assassination attempts are a reminder that better legislation is needed
In early August an assassination attempt on Venezuelan President Nicolas Maduro served as a jarring wake up call that the possibility of a drone attack against a public figure or civilian is real. дальше »
2018-11-17 17:30 | |
|
|
2FA codes are great for security, except when 26M of them are leaked
Just when you thought two-factor authentication was enough to secure your online accounts, a troubling discovery shows how this system can be comprised, thanks to human error. TechCrunch reports that a database of text messages containing more than 26 million 2FA codes, password reset links, and delivery tracking details was left out in the open … This story continues at The Next Web дальше »
2018-11-16 13:22 | |
|
|
Target blames Bitcoin scam tweet on third-party app, not Twitter
American retail behemoth Target has come out to clarify that a tweet it posted, containing a link to a Bitcoin giveaway scam, came from a third-party software provider – not Twitter. In an email to Hard Fork, a company spokesperson said – contrary to what it suggested previously – Target’s Twitter account was never inappropriately accessed. дальше »
2018-11-15 14:12 | |
|
|
More malicious cryptocurrency apps found on the Play Store
It seems we might never win the battle against fake cryptocurrency apps on Google’s Play Store, as another four have been identified this week. The apps were masquerading on the Play Store as cryptocurrency wallets for NEO, Tether, and MetaMask. дальше »
2018-11-14 18:09 | |
|
|
Twitter Has a Hard Time Dealing with Hackers, as New Bitcoin Scams Target Target
Despite the increased security efforts, Twitter is still unable to weed out scam accounts, as U. S. retail giant Target became the latest victim of bitcoin scam hacks, The Next Web reported on November 13, 2018. дальше »
2018-11-14 16:00 | |
|
|
Alex Jones’ Infowars store was infected with credit card skimming software
Infowars is best known as the fake news platform used by beetroot-red nutjob Alex Jones to spout wild conspiracies and defame grieving parents. But did you also know it boasts an online store where you can buy vitamins, “neutraceuticals,” and garish right-wing t-shirts? I mention the retail bit because, according to ZDNet and Dutch security researcher, Willem de Groot, it was recently the site of a particularly nasty Magecart infection, which hoovered up the details of roughly 1,600 customers. дальше »
2018-11-14 12:59 | |
|
|
Facebook bug allowed websites to grab unsuspecting users’ personal data
Security firm Imperva found a bug in May that allowed websites to read Facebook users and their friends’ private information. The troubling vulnerability let a site access users’ likes and interests through a manipulated Facebook Graph query. дальше »
2018-11-14 09:24 | |
|
|
Here’s why it is unsurprising that China, the US, and Russia didn’t sign the global cyber security pact
On Monday, French President Emmanuel Macron released an international agreement on cyber security principles at the Paris Peace Forum. While the pact was signed by 51 countries, 130 global companies and 90 charitable groups and universities, the five most notorious countries in cyber warfare refused to sign. дальше »
2018-11-14 22:44 | |
|
|
Apple confirms its T2 chip will block some third-party repairs
Apple yesterday confirmed that its new security chip T2 – which it uses in MacBooks launched this year – will prevent third-party repairs to some degree. Responding to a query from The Verge, the company verified that parts like the logic board and Touch ID components for the new Macbooks can’t be replaced by a third-party repair shop – and so you’ll have to visit an authorized Apple service center to get your laptops fixed. дальше »
2018-11-13 09:39 | |
|
|
5 recent tactics criminals use to steal your Bitcoin (and other cryptocurrency)
While the cryptocurrency mania that drove Bitcoin’s price to $20,000 may have eased, the threat posed by the most experienced cybercriminals hasn’t disappeared. In fact, prominent information security firm Kaspersky Labs has detailed how some of the internet’s most well-known cyberthreats have evolved to better target cryptocurrency users and services. дальше »
2018-11-12 17:47 | |
|
|
Security Token Offerings – The Next Big Thing In Crypto?
If you are not familiar with security token offerings (STOs), maybe you should be. With regulators gunning for initial coin offerings (ICOs) and now going after decentralised exchanges (DEXs) too, industry players are looking at news ways of raising money. дальше »
2018-11-11 22:22 | |
|
|
eToro rolls out its cryptocurrency wallet for Android and iOS
Social trading platform eToro has finally begun rolling out its cryptocurrency wallet to Android and iOS users. The wallet, which promises an intuitive customer interface and enhanced security, is now available on Google Play and Apple’s App Store. дальше »
2018-11-8 19:54 | |
|
|
Hackers hide cryptocurrency mining malware in Windows installation files
Crypto-jacking schemes are getting more intricate by the day. It appears hackers are now disguising cryptocurrency mining malware and passing it off as legitimate Windows installation packages. дальше »
2018-11-8 18:20 | |
|
|
University shuts down its entire network to stop Bitcoin crypto-jackers
A Canadian university had to shut down its entire campus network after it discovered hackers had hijacked its computing power to surreptitiously mine cryptocurrency – Bitcoin, to be exact. In a statement released earlier this week, Nova Scotia-based St. дальше »
2018-11-7 13:44 | |
|
|
20,000 Pakistani debit card details surface on the dark web
On Tuesday, Pakistan’s Federal Investigation Agency (FIA) said that major banks in the country have suffered a cyber attack affecting more than 20,000 users. “More than 100 cases (of cyber-attack) have been registered with the FIA and are under investigation. дальше »
2018-11-7 12:08 | |
|
|
Researchers rank cryptocurrency exchanges by how secure they are
Prominent cyber-security firm Group-IB has graded the security of online cryptocurrency exchanges, as a means of assessing insurance risk. It found long-standing platform Kraken to be the most secure, with OKEx, Huobi Pro, and CoinCheck among the riskiest. дальше »
2018-11-6 20:10 | |
|
|
8 expert predictions on what will define tech in 2019
If you’re a tech junkie, you’ve inevitably thought about what it would be like to run into your future self, even just a year from now. What apps would be on your phone? How would your user experience change? What’s the next big thing you won’t be able to imagine your life without? To find out we went to this year’s EIT Digital Challenge where some of Europe’s finest deep tech scaleups and late-stage startups were pitching cutting-edge solutions that will innovate everything from online security to our own personal well-being (see all 10 winners here). дальше »
2018-11-6 15:19 | |
|
|
Moonday Mornings: Intel CPU weakness could compromise cryptocurrency private keys
We spent the entire weekend failing to reach the bottom of our buckets of Halloween candy. Yes, we’re disappointed with ourselves too. But as it’s Moonday, we’ve put that aside and rounded up the best cryptocurrency news from the last few days just for you! Here’s some of our top picks. дальше »
2018-11-5 12:02 | |
|
|
Google Play app caught phishing for cryptocurrency exchange login details
Despite Google’s hardline stance against malicious cryptocurrency apps, some still find ways of sneaking through its net. Security and malware researcher, Lukas Stefanko, published a video yesterday exposing how a malicious app, distributed via Google’s Play Store, steals the sensitive data from unsuspecting users. дальше »
2018-11-2 17:55 | |
|
|
Blockchain Brainiac Says Serenity Upgrade Will Give Ethereum 1,000x Increase In Transactions Per Second
Serenity Upgrade Will Give Ethereum Thousand Fold Increase In Transactions Per Second Vitalik Buterin, the co-founder of Ethereum, told an audience in Prague that the network is preparing for the next upgrade to the second largest blockchain network. дальше »
2018-11-1 20:00 | |
|
|
This Day in Deals: ‘Magic’ security cameras for evading sorcerers
This Day In Deals is our new section where we share a historical fact and the day’s best deal – and try to connect them. The aim? To enrich ourselves financially, and you spiritually. The Tempest might not be Shakespeare’s best-known play, but it’s one of my favorites. дальше »
2018-11-1 14:44 | |
|
|
Police are outsourcing criminal-catching to IoT in Dutch ports
The Internet of Trucks is here. Or, to be, more specific: the internet of tarpaulins. Industrial textile company Sioen is currently developing smart truck tarpaulins that notify security when someone tries to cut through it. дальше »
2018-11-1 11:29 | |
|
|